Intelligence Context
The Intelligence Context section expands on the network of agencies and research facilities that underpin the novel’s cyber operations. While dramatized, this framework reflects genuine overlaps between military, intelligence, and industrial interests inside modern nation-state cyber programs.
-
1 State Council / Party Guidance OversightStrategic direction and prioritization at the national level.
-
Counterintelligence and cover entities channel tasking and access.
-
3 PLA — JSD, SSF, Unit 61398 PLAOperational lift and technical infrastructure supporting cyber activity.
-
Operational cell executes research and exploitation with cover entities.
-
5 Tasking → Support → Execution FlowTasking routes through fronts; SSF/61398 provide technical support to FAC‑17.
MSS / PLA Integration
Within the novel, Facility 17 (“FAC-17”) operates at the junction of state security and military research. Tasking flows from MSS headquarters through fronts that obscure technical sponsorship, while Unit 61398 and the Strategic Support Force provide infrastructure and manpower. Inside that web are scientists, engineers, and analysts who see themselves not as villains, but as professionals protecting national capability.
Operational Reality
Many of the real organizations behind this fictional architecture have operated for decades under shifting names and missions. The Ministry of State Security was formalized in the early 1980s, built from older internal security bureaus, while PLA cyber and signals units—most visibly Unit 61398—surfaced publicly in the 2000s after years of quieter technical buildup. Their continuity underscores how modern cyber operations aren't sudden inventions but long-mature systems adapting to new tools.
The people inside those institutions—mathematicians, linguists, coders, and field officers—carry their own worldviews, shaped by duty, pressure, and history. Portraying them as two-dimensional adversaries would miss the point; the novel’s aim is to show how conviction and expertise can coexist with blind spots, and how every system believes it’s safeguarding something worth keeping.
The portrayal of intelligence coordination in Dark Recipe isn't an accusation. It's an examination of how large systems—national or corporate—can evolve past their creators' control while still believing they serve a higher purpose.
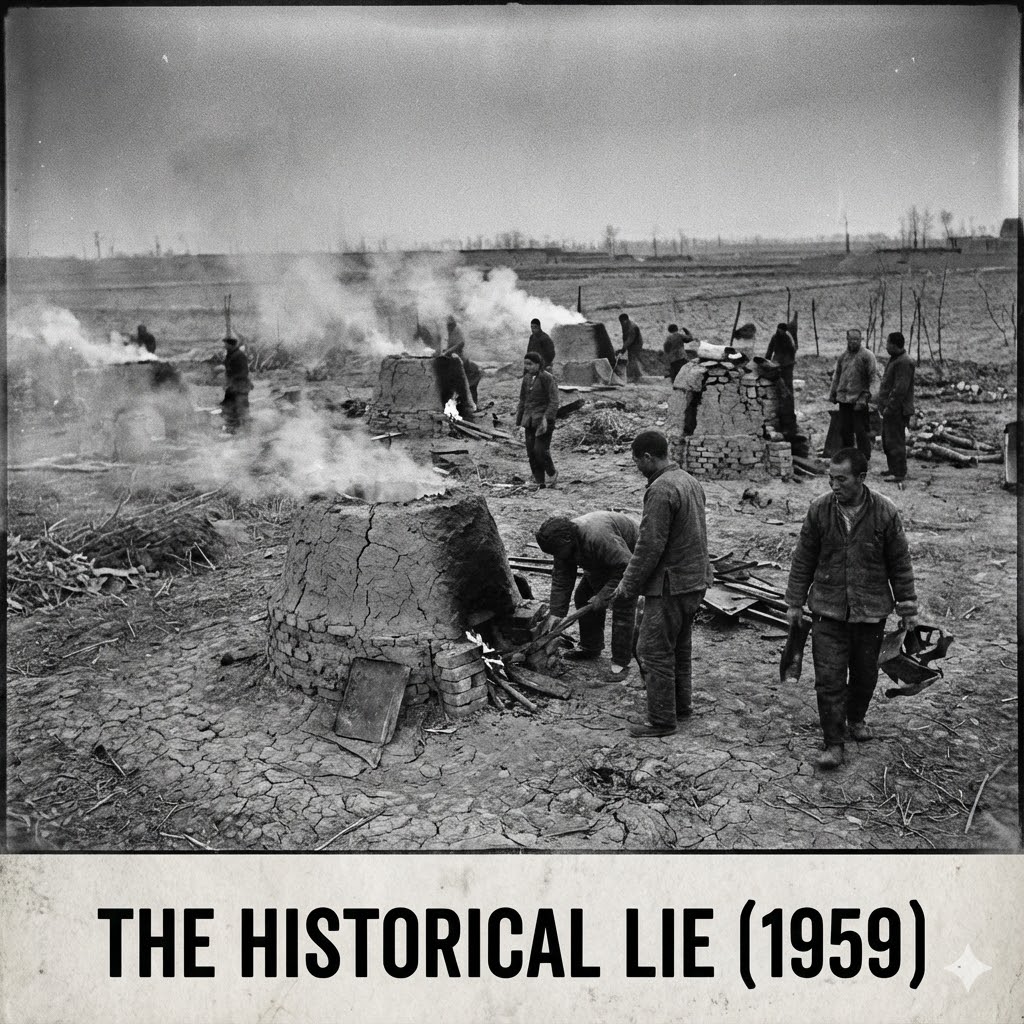
Historical Parallel: The Lessons of 1959
The "Historical Lie" image references the beginning of the Great Chinese Famine (1959–1961)—not a natural disaster, but a system failure. It was a man-made catastrophe driven by bad data, political pressure to ignore reality, and pseudoscience. For readers of Dark Recipe, these three failures mirror the novel's premise with unsettling precision.
1. The Ecological Error: "Four Pests Campaign"
The Logic: The government calculated that sparrows ate grain seeds. Kill a million sparrows, save enough grain to feed 60,000 people.
The Execution: Citizens banged pots and pans for days so birds couldn't land, eventually dropping dead from exhaustion.
The Result: Sparrows also ate insects. With the birds gone, locusts swarmed and destroyed the crops the sparrows would have protected.
Connection to Dark Recipe: The corrupted optimization algorithms manipulate plant defense chemistry—the modern equivalent of "breaking the biological balance" to achieve efficiency, only to cause catastrophe.
2. The Scientific Error: "Lysenkoism"
The Logic: China adopted Soviet agronomist Trofim Lysenko's theory that plants of the same "class" would help rather than compete with each other.
The Execution: Farmers plowed soil 2-3 meters deep (damaging topsoil) and planted seeds 5-10x denser than normal.
The Result: Seedlings overcrowded. Air couldn't circulate, sunlight couldn't reach stems, crops rotted. From a distance, fields looked thick and lush—the illusion of success—but inside, they were dead.
Connection to Dark Recipe: This is the direct ancestor of Operation Harvest Cloud—using "bad science" (corrupted optimization loops) to force plants into unnatural states that appear successful while producing poison.
3. The Data Error: "The Wind of Exaggeration"
The Logic: Local officials were terrified of failing to meet production quotas set by Beijing.
The Execution: When crops failed, officials lied. They reported "record-breaking" harvests to the central government.
The Result: Beijing believed the data. They calculated taxes based on the fake numbers and sent trucks to collect what they thought was a small percentage of a "bumper crop." They took the village's entire actual harvest. Farmers were left with nothing.
Connection to Dark Recipe: FarmLytics provides "flawless, cryptographically clean audit trails" while the food is actually poison. The exact same mechanism: the data says everything is fine while the people are dying.
"In 1959, they tried to engineer nature without understanding it. They killed the birds, they faked the data, and they broke the soil. Forty million people died because the system refused to accept reality.
Operation Harvest Cloud is that same system, weaponized against us."
Compiled from research notes, interviews, and open-source intelligence — 2025 edition
Analyst Notes
Operational cells at FAC-17 receive tasking via fronts and cover entities. Technical lift (SIGINT/cyber) flows from Unit 61398 through SSF channels. The novel dramatizes bureaucratic friction inside this structure.